|
|
(Swift) Sign PDF and Provide Certificates in Chain to Root
Discusses how to provide certificates in the chain of authentication to the root certificate if the certs are not available to Chilkat.
If you provided a .p12 or .pfx, then it is likely the .p12/.pfx already contains the certs in the chain of authentication, and Chilkat will automatically find them.
Also, if running on a Windows system, then Chilkat will likely automatically find the intermediate CA certs and root CA cert as needed.
This example demonstrates how to explicitly provide the CA certs in the chain of authentication to any Chilkat application that is signing.
Note: This example requires Chilkat v9.5.0.92 or greater.
func chilkatTest() {
// This example requires the Chilkat API to have been previously unlocked.
// See Global Unlock Sample for sample code.
// Assuming you don't have the intermediate CA and root CA certificates for the chain of authentication, then you'll need to locate them from your CA, download, and then use as shown below.
// For example, if your certificate has this certification path:
// 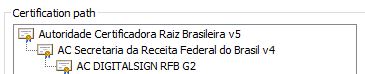 // Then you should Google "AC DIGITALSIGN RFB G2".
// In this case, the resulting URL found by Google is: https://www.digitalsigncertificadora.com.br/repositorio/RFB
// You can download the certs from https://www.digitalsigncertificadora.com.br/repositorio/rfb/ACDIGITALSIGNRFB.p7b
// Load the certs from a .p7b into an XML certificate vault.
// Note: This example requires Chilkat v9.5.0.92 or greater. The ability to load .p7b files containing multiple certificates was added in v9.5.0.92
let vault = CkoXmlCertVault()!
var success: Bool = vault.addCertFile("qa_data/certs/ACDIGITALSIGNRFB.p7b")
if success == false {
print("\(vault.lastErrorText!)")
return
}
// -----------------------------------
// See how the vault is used below...
// -----------------------------------
// The signed PDF produced by this example should be verifiable at https://verificador.iti.gov.br/verifier-2.6.2/
let pdf = CkoPdf()!
// Load a PDF to be signed.
// The "hello.pdf" is available at https://chilkatsoft.com/hello.pdf
success = pdf.loadFile("qa_data/pdf/hello.pdf")
if success == false {
print("\(pdf.lastErrorText!)")
return
}
let json = CkoJsonObject()!
// Define the appearance and location of the signature.
json.updateInt("page", value: 1)
json.update("appearance.y", value: "bottom")
json.update("appearance.x", value: "middle")
json.update("appearance.fontScale", value: "9.0")
json.update("appearance.text[0]", value: "Digitally signed by: cert_cn")
json.update("appearance.text[1]", value: "current_dt")
json.update("appearance.image", value: "document-accepted")
json.update("appearance.imagePlacement", value: "left")
json.update("appearance.imageOpacity", value: "100")
// Add the CMS options required for ICP-Brasil
json.updateInt("contentType", value: 1)
json.updateInt("messageDigest", value: 1)
json.updateInt("signingCertificateV2", value: 1)
// Listed here are the currently existing profiles. (Chilkat will add additional ICP Brasil policy profiles in future versions as new ones are created.)
// See https://www.gov.br/iti/pt-br/assuntos/repositorio/artefatos-de-assinatura-digital for more information.
//
// PA_PAdES_AD_RA_v1_0 --> 2.16.76.1.7.1.14.1
// PA_PAdES_AD_RA_v1_1 --> 2.16.76.1.7.1.14.1.1
// PA_PAdES_AD_RA_v1_2 --> 2.16.76.1.7.1.14.1.2
// PA_PAdES_AD_RB_v1_0 --> 2.16.76.1.7.1.11.1
// PA_PAdES_AD_RB_v1_1 --> 2.16.76.1.7.1.11.1.1
// PA_PAdES_AD_RC_v1_0 --> 2.16.76.1.7.1.13.1
// PA_PAdES_AD_RC_v1_1 --> 2.16.76.1.7.1.13.1.1
// PA_PAdES_AD_RC_v1_2 --> 2.16.76.1.7.1.13.1.2
// PA_PAdES_AD_RT_v1_0 --> 2.16.76.1.7.1.12.1
// PA_PAdES_AD_RT_v1_1 --> 2.16.76.1.7.1.12.1.1
// Set the policy OID and the profile name
json.update("policyId.id", value: "2.16.76.1.7.1.11.1.1")
json.update("policyId.profile", value: "PA_PAdES_AD_RB_v1_1")
// Also explicitly set the filter and subFilter
json.update("filter", value: "Adobe.PPKLite")
json.update("subFilter", value: "adbe.pkcs7.detached")
// Load the signing certificate.
// In this example, we'll load from a source where we don't have the certificates in the chain.
let cert = CkoCert()!
success = cert.load(fromSmartcard: "")
if success == false {
print("\(cert.lastErrorText!)")
return
}
// ------------------------------------------------------------------------------------------
// Here's where we make the certificates in the chain of authentication available to Chilkat.
// If the certs in the chain of authentication are available in the vault, then Chilkat will
// automatically find them as needed.
// ------------------------------------------------------------------------------------------
success = cert.use(vault)
// Also, tell the PDF object we want to include certs in the chain of authentication to the root, if possible.
json.updateBool("embedCertChain", value: true)
json.updateBool("includeRootCert", value: true)
// Tell the pdf object to use the certificate for signing.
success = pdf.setSigning(cert)
if success == false {
print("\(pdf.lastErrorText!)")
return
}
success = pdf.sign(json, outFilePath: "qa_output/hello_signed.pdf")
if success == false {
print("\(pdf.lastErrorText!)")
return
}
print("\(pdf.lastErrorText!)")
print("The PDF has been successfully cryptographically signed.")
}
// Then you should Google "AC DIGITALSIGN RFB G2".
// In this case, the resulting URL found by Google is: https://www.digitalsigncertificadora.com.br/repositorio/RFB
// You can download the certs from https://www.digitalsigncertificadora.com.br/repositorio/rfb/ACDIGITALSIGNRFB.p7b
// Load the certs from a .p7b into an XML certificate vault.
// Note: This example requires Chilkat v9.5.0.92 or greater. The ability to load .p7b files containing multiple certificates was added in v9.5.0.92
let vault = CkoXmlCertVault()!
var success: Bool = vault.addCertFile("qa_data/certs/ACDIGITALSIGNRFB.p7b")
if success == false {
print("\(vault.lastErrorText!)")
return
}
// -----------------------------------
// See how the vault is used below...
// -----------------------------------
// The signed PDF produced by this example should be verifiable at https://verificador.iti.gov.br/verifier-2.6.2/
let pdf = CkoPdf()!
// Load a PDF to be signed.
// The "hello.pdf" is available at https://chilkatsoft.com/hello.pdf
success = pdf.loadFile("qa_data/pdf/hello.pdf")
if success == false {
print("\(pdf.lastErrorText!)")
return
}
let json = CkoJsonObject()!
// Define the appearance and location of the signature.
json.updateInt("page", value: 1)
json.update("appearance.y", value: "bottom")
json.update("appearance.x", value: "middle")
json.update("appearance.fontScale", value: "9.0")
json.update("appearance.text[0]", value: "Digitally signed by: cert_cn")
json.update("appearance.text[1]", value: "current_dt")
json.update("appearance.image", value: "document-accepted")
json.update("appearance.imagePlacement", value: "left")
json.update("appearance.imageOpacity", value: "100")
// Add the CMS options required for ICP-Brasil
json.updateInt("contentType", value: 1)
json.updateInt("messageDigest", value: 1)
json.updateInt("signingCertificateV2", value: 1)
// Listed here are the currently existing profiles. (Chilkat will add additional ICP Brasil policy profiles in future versions as new ones are created.)
// See https://www.gov.br/iti/pt-br/assuntos/repositorio/artefatos-de-assinatura-digital for more information.
//
// PA_PAdES_AD_RA_v1_0 --> 2.16.76.1.7.1.14.1
// PA_PAdES_AD_RA_v1_1 --> 2.16.76.1.7.1.14.1.1
// PA_PAdES_AD_RA_v1_2 --> 2.16.76.1.7.1.14.1.2
// PA_PAdES_AD_RB_v1_0 --> 2.16.76.1.7.1.11.1
// PA_PAdES_AD_RB_v1_1 --> 2.16.76.1.7.1.11.1.1
// PA_PAdES_AD_RC_v1_0 --> 2.16.76.1.7.1.13.1
// PA_PAdES_AD_RC_v1_1 --> 2.16.76.1.7.1.13.1.1
// PA_PAdES_AD_RC_v1_2 --> 2.16.76.1.7.1.13.1.2
// PA_PAdES_AD_RT_v1_0 --> 2.16.76.1.7.1.12.1
// PA_PAdES_AD_RT_v1_1 --> 2.16.76.1.7.1.12.1.1
// Set the policy OID and the profile name
json.update("policyId.id", value: "2.16.76.1.7.1.11.1.1")
json.update("policyId.profile", value: "PA_PAdES_AD_RB_v1_1")
// Also explicitly set the filter and subFilter
json.update("filter", value: "Adobe.PPKLite")
json.update("subFilter", value: "adbe.pkcs7.detached")
// Load the signing certificate.
// In this example, we'll load from a source where we don't have the certificates in the chain.
let cert = CkoCert()!
success = cert.load(fromSmartcard: "")
if success == false {
print("\(cert.lastErrorText!)")
return
}
// ------------------------------------------------------------------------------------------
// Here's where we make the certificates in the chain of authentication available to Chilkat.
// If the certs in the chain of authentication are available in the vault, then Chilkat will
// automatically find them as needed.
// ------------------------------------------------------------------------------------------
success = cert.use(vault)
// Also, tell the PDF object we want to include certs in the chain of authentication to the root, if possible.
json.updateBool("embedCertChain", value: true)
json.updateBool("includeRootCert", value: true)
// Tell the pdf object to use the certificate for signing.
success = pdf.setSigning(cert)
if success == false {
print("\(pdf.lastErrorText!)")
return
}
success = pdf.sign(json, outFilePath: "qa_output/hello_signed.pdf")
if success == false {
print("\(pdf.lastErrorText!)")
return
}
print("\(pdf.lastErrorText!)")
print("The PDF has been successfully cryptographically signed.")
}
|

